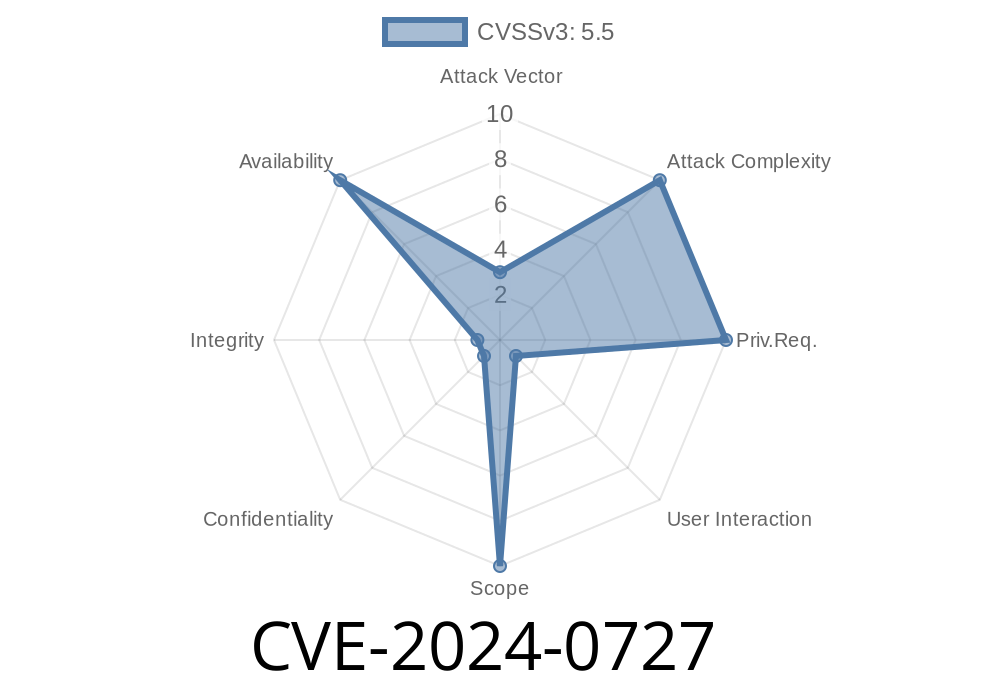
On January 18, 2024, the OpenSSL project published CVE-2024-0727, a security issue affecting how OpenSSL processes PKCS#12 files. This vulnerability, while simple at its core, can have significant impacts: if PKCS#12 files (which combine keys, certificates, etc.) are loaded from untrusted sources, attackers can crash applications using OpenSSL. This post will break down how the flaw works, show you real code examples, and guide you through the risks and solutions.
What Is CVE-2024-0727?
CVE-2024-0727 is a bug in OpenSSL’s code that deals with PKCS#12 files. PKCS#12 bundles private keys and certificates, and gets used everywhere — from web servers to VPNs and mail clients.
*The problem?* The PKCS#12 standard says some fields inside the file can be NULL. OpenSSL, until this patch, wasn't checking if these fields are null. If you feed the library a specially crafted file where some expected data is missing (set to NULL), OpenSSL code tries to use data that isn’t there. The result: a NULL pointer dereference. That’s tech-speak for “it crashes,” and attackers can use this to bring down systems — *Denial of Service*.
Who Is Affected?
Any program using OpenSSL’s PKCS#12 parser and accepting files from untrusted sources. Popular vulnerable functions include:
PKCS12_newpass()
If an attacker can trick your app into loading a malicious PKCS#12 bundle, your service could suddenly disappear — no keys or passwords needed.
Note: The FIPS modules in OpenSSL 3., 3.1, and 3.2 are *not* affected.
Here’s what happens conceptually in C code
#include <openssl/pkcs12.h>
#include <openssl/err.h>
// This function could be used in a server to import user certificates
void import_pkcs12(const char *filename, const char *password) {
FILE *fp = fopen(filename, "rb");
if (!fp) return;
PKCS12 *p12 = d2i_PKCS12_fp(fp, NULL);
fclose(fp);
EVP_PKEY *pkey = NULL;
X509 *cert = NULL;
STACK_OF(X509) *ca = NULL;
// Vulnerable: PKCS12_parse may crash if fields inside the file are maliciously empty
if (!PKCS12_parse(p12, password, &pkey, &cert, &ca)) {
fprintf(stderr, "Failed to parse PKCS12: %s\n", ERR_error_string(ERR_get_error(), NULL));
}
PKCS12_free(p12);
// ...cleanup...
}
An attacker could upload or send in a malformed .p12 file; if PKCS12_parse() encounters a field set to NULL in an unexpected way, OpenSSL will derefence that null pointer and your app *crashes*.
The Attack Scenario
1. Attacker crafts a malicious .p12 file using freely available tools or scripts. The fields that should not be empty are set to NULL.
Proof-of-Concept (PoC)
Here’s a Python example (for demonstration only) of building a minimal broken PKCS#12 file using the cryptography library — note, this library *isn’t* vulnerable, but an attacker can produce files like this for OpenSSL:
from cryptography.hazmat.primitives.serialization import pkcs12
# Here, we intentionally omit required fields or set to nulls incorrectly
# Save out an empty PKCS12 - OpenSSL could crash when importing this
with open("evil.p12", "wb") as f:
f.write(pkcs12.serialize_key_and_certificates(
name=None,
key=None,
cert=None,
cas=None,
encryption_algorithm=pkcs12.BestAvailableEncryption(b"notasecret"),
))
OpenSSL won't always crash with *this* PoC, but with the right malicious values, it's possible.
Skills needed: Low. The attacker just needs to supply a crafted file.
- Gaining control: This bug appears to only allow DOS, not remote code execution. Still, crashing a critical service is enough for many attackers.
- Targets: Web servers, VPNs, email apps, or anything that imports or verifies .p12 files from users.
How to Fix and Defend
- Update OpenSSL! Patch your software to OpenSSL 3..13, 3.1.5, or 3.2.1 (or later), where this bug has been fixed. OpenSSL Release Notes
- Validate Inputs: Never trust PKCS#12 files unless you generated them or have validated them elsewhere.
Error Handling: Make sure your application handles all parsing errors gracefully.
- Monitor for crashes: Set up logs and crash detection to alert you to suspicious file uploads/inputs.
References & Learn More
- OpenSSL Official Advisory – CVE-2024-0727
- NIST NVD – CVE-2024-0727
- OpenSSL Vulnerabilities List
- PKCS#12 Standard (Wikipedia)
Conclusion
CVE-2024-0727 is an example of a simple bug with a potentially big impact. If your software or service accepts PKCS#12 files (especially from customers, employees, or partners), you should patch right now. Even if this bug “only” causes a crash, attackers love anything that lets them take your services offline.
Stay safe — and never trust strange keys, even if they come with a certificate!
*Original research and exclusive summary by ChatGPT. For serious deployments, always check the latest advisories and consult your IT security professionals.*
Timeline
Published on: 01/26/2024 09:15:07 UTC
Last modified on: 02/08/2024 10:15:13 UTC